The NBA, NFL and MLB have all taken proactive steps to upgrade and strengthen security at stadiums and arenas across the nation. The NBA, for example, in 2017 mandated that all new and existing facilities be updated to meet or exceed the regulations as outlined in the NBA Arena Standards Manual.
 Joseph T. Dyer is a senior associate and project manager with Perkins+Will, and Ross B. Cussen is a protective design and security engineer with Thornton Tomasetti.
Joseph T. Dyer is a senior associate and project manager with Perkins+Will, and Ross B. Cussen is a protective design and security engineer with Thornton Tomasetti.
Evolving security threats have forced facility owners, operators and tenants at every level to reassess the security of sports venues. Determining the security design criteria for a new project or identifying the most pressing security needs for an existing facility can be daunting. Communicating with owners, operators, stakeholders and law enforcement is the initial step in providing venue safety. From there, consultants who specialize in security planning, client coordination and advanced visualization for any number of security scenarios can be key in developing appropriate risk mitigation solutions, as well as crisis management planning and training.
A range of security threats and scenarios should be considered in the design of new facilities to enable a dynamic perimeter security program. The vulnerabilities at existing facilities should be assessed in terms of their ultimate risk to the venue, and the facilities modified to reduce risks deemed unacceptable by stakeholders.
Detect, deter, deny, delay
The perimeter of a facility is the most important layer in a well-established security program, offering opportunities to detect, deter, deny or delay a potential attack. The perimeter therefore should be the most refined aspect of a security program. Given that every facility is unique, there isn't a one-size-fits-all approach to perimeter security at sports venues. Security measures must balance the facility's aesthetics, the experience of the fans, and the needs of venue staff and athletes with the need to create a safe and secure environment.
The first step in any evaluation of a facility's perimeter is to perform an assessment of the existing or planned conditions. This risk assessment can take the form of a security audit for smaller existing facilities with established security programs, or a more comprehensive threat, vulnerability and risk assessment (TVRA) for major facilities or new design/build projects. While TVRAs can be conducted for existing facilities and for planned facilities, it is recommended that an assessment be conducted at the outset of any intended design work so that the suggestions of the assessment can be incorporated into the overall project as seamlessly as possible.
In addition to the empirical knowledge of an established and objective security consultant, a number of sports governing bodies publish internal security standards that can be considered during the TVRA process. Other stakeholders, such as the local municipality, educational institution, and local first responders (law enforcement, fire, and emergency medical services) may also be involved in the process.
A modern protected perimeter incorporates physical, technical and operational security elements in varying combinations to create the first layer in a secure environment. Physical security elements may include fences, walls, landscaping, terrain, vehicle barriers, and blast or ballistic protection elements. Technical security elements include cameras, intrusion detection systems, electronic and mechanical access control, personnel and vehicle screening equipment, as well as other electronic security measures. Operational security measures include staff training procedures, bag check policies, facilities rules of conduct for patrons, explosive detection, and drug canine screening.
Ultimately, decisions regarding which security measures to implement are made by the facility owner/operator/tenant once all relevant factors have been considered. It is impossible to eliminate all risks; therefore, design features and upgrades should be selected using a cost-benefit methodology to provide the greatest overall risk reduction. Here are three primary categories of venue perimeter threat mitigation:
![[Photo courtesy of Kay Park-Rec Corp.]](https://img.athleticbusiness.com/files/base/abmedia/all/image/2019/08/ab.safety719a.png?auto=format%2Ccompress&fit=max&q=70&w=400) [Photo courtesy of Kay Park-Rec Corp.]
[Photo courtesy of Kay Park-Rec Corp.]
1. Hostile vehicle mitigation
A common feature of an athletic facility's perimeter security program is to provide hostile vehicle mitigation (HVM). Hostile vehicle threats include vehicle-borne improvised explosive devices (VBIED), use of the vehicle as a weapon (VAW), and unintentional vehicle collisions or sidewalk intrusions. All variances of vehicle threats stress the need to maintain a safe vehicle standoff distance from the facility as well as from areas of high pedestrian density outside the facility. Potential types and locations of vehicle threats that should be considered in the design are typically outlined in the TVRA.
Assessment of the site layout and geometry will generate design solutions that can range from configuration of roadways and parking lots to avoid high-speed approaches to providing crash-tested barriers such as bollards and walls at critical areas outlined in the TVRA. Critical areas may include areas of high patron density (entrance locations) or locations adjacent to critical infrastructure, such as utility points of entry, generators and fuel storage.
Crash-rated barriers are designed and tested to comply with certain standards. They are designed to absorb substantial amounts of energy and require robust structural properties and foundations. For new facilities, the perimeter design should take into account the aesthetics of these barriers, plan for their location, and coordinate their sizes with underground utilities and other obstructions to achieve seamless integration within the overall facility design. For existing facilities, custom barrier designs are often required to accommodate existing site conditions to best reduce potential hostile threats.

2. Pedestrian security screening
Screening and control of pedestrians entering and exiting the facility is another important aspect of perimeter security. Screening operations must provide a prudent level of security and enable an efficient rate of throughput for operations, while also maintaining a pleasant fan experience. A range of policies can be implemented to prevent weapons or other contraband from being brought into the facility. Bag policies, bag checks and user education are the simplest measures to implement. However, to be effective, training and technology should accompany physical screening operations. Technology that can be implemented includes handheld metal detectors, walkthrough magnetometers and x-ray machines.
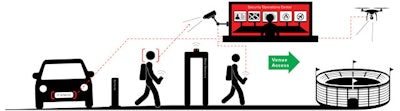
3. Concealed shooter and drone threat assessment
Perimeter security was largely assessed two-dimensionally prior to the October 2017 shooting incident in Las Vegas. This incident highlighted the risk to venues from concealed shooter threats stationed at locations vertically above and adjacent to targets. These types of threats exist in many urban facilities surrounded by public spaces and buildings.
To identify options to mitigate this threat, a counter-concealed shooter assessment (CCSA) can be performed to examine vulnerable lines of sight from surrounding areas into the populated areas of the venue. Once vulnerabilities have been identified, the facility security program can be designed or modified to mitigate these risks by blocking lines of sight, providing ballistic-resistant barriers, redeploying perimeter security staffing or developing memorandums of understanding (MOUs) with adjacent properties to secure vulnerable line-of-sight platforms during events.
Additionally, drones have forced security planners to assess threats from the air, with some facilities implementing drone detection systems to identify the location of a drone operator through the tracing of radio frequency signals between the operator console and the drone itself. Further, drones have been utilized overseas as a mechanism to deploy more traditional weapons like firearms and explosives in an effort to bypass ground-level perimeter security.
Emerging perimeter technologies
The amalgamation of the three categories above contributes to the changing environment for security planners in establishing an effective perimeter security program.
Other technological systems can be implemented to assist security staff with identifying and responding to security threats. These systems can include video analytics to identify unauthorized intrusions through the perimeter (e.g., movement or geofencing) or bags that have been left behind in unscreened areas. The response to active shooter incidents may include technology to quickly identify the location of the adversary and initiate an efficient and effective response. Gunshot detection systems have been successfully deployed at facilities around the nation and can help to immediately identify the location of an incident and transmit this information to facility security staff and local law enforcement for their situational awareness and response.
As highlighted during the 2017 Manchester Arena bombing, the security perimeter needs to be maintained before, during and after an event. In this paradigm-shifting security incident, fans were attacked while exiting the facility. Crowd evacuation modeling software can be used to predict crowd movement and response to security incidents. Resulting analytics can then identify choke points and vulnerabilities along exiting paths.
The perimeter security of any athletic facility — from youth sports venues up to professional sports stadiums and arenas — can be enhanced by determining existing vulnerabilities and implementing physical, technical and/or operational security measures to mitigate the greatest risks. Focusing on the perimeter reduces potential threats from ever entering the facility and stops the risk at the point of attack.
This article originally appeared in the July | August 2019 issue of Athletic Business with the title "How to strengthen your facility’s perimeter security." Athletic Business is a free magazine for professionals in the athletic, fitness and recreation industry. Click here to subscribe.